Mutual Authentication and Session Key Establishment for Secure Communication using Generalized Digital Certificate
Автор: Balaji V Durgawad, Mohammed Aijaz Ahmed, D. Rajya Lakshmi, Sayed Abdul Sattar
Журнал: International Journal of Computer Network and Information Security(IJCNIS) @ijcnis
Статья в выпуске: 8, 2017 года.
Бесплатный доступ
Public–key digital certificates are being used in public key infrastructure to provide authentication of the user's public key. Public key digital certificates like X.509 are used to bind a public key to its user. This kind of certificates cannot be used for user authentication. Such use may lead to forgery of user's identity. Lein et al proposed a authentication scheme based on Generalized Digital Certificates (GDC). A GDC consists of user's public information like digital birth certificate, digital identity, etc. and the digital signature of trusted third party generated from that public information. The GDC based scheme provides user authentication and allows for session key establishment. The scheme is secure against forgery of user's identity but it does not provide mutual authentication. The scheme proposed in this paper not only provides mutual authentication and session key but also it preserves the security strength of Lein et al's GDC based scheme.
PKI, public key digital certificate, generalized digital certificate, identity forgery, authentication and session key
Короткий адрес: https://sciup.org/15011871
IDR: 15011871
Текст научной статьи Mutual Authentication and Session Key Establishment for Secure Communication using Generalized Digital Certificate
Public key digital certificate consists of a public key of certificate holder, name, period of validity, algorithm, etc. and digital signature generated for this public key [18]. The digital signature is generated by trusted third party normally certifying authority (CA). “X.509” is an example of public key digital certificate [1]. In PKI X.509 certificate is widely used to provide authentication of Certificate holder’s public key. If a certificate holder proves that he has knowledge of the private key associated with the public key specified in the X.509 digital certificate the certificate holder is authenticated otherwise not.
But there is a security flaw identified in this mechanism. As all fields present in public key digital certificate are public, if a malicious receiver obtains public key digital certificate, then he can forge the identity of the certificate holder. If a certificate holder H needs to send a message M to J, then H will create a message M and put his digital signature SIGNH on it using private key PRH and encrypts it by using the public key PUJ and then forwards this digitally signed and encrypted message to J. J will decrypt it using J’s private key PRJ. Then J will verify the digital signature SIGNH of certificate holder H. For this J needs a public key PUH of H which is obtained from public key digital certificate of H. If the digital signature SIGNH of H verified correctly, then J comes to know that the message received is really coming from H. If receiver J is not trustworthy, then he can encrypt the digitally signed message by H using public key PUX of other user X and forwards this message to X. Then X will decrypt it using its private key PRX. X finds a digital signature SIGNH and needs to verify the digital signature SIGNH of certificate holder H. For this J needs a public key PUH of H which is obtained from public key digital certificate of H. If the digital signature SIGNH of H verified correctly, then X comes to know that the message received is really coming from H. But it is not true. Thus the identity of certificate holder H is forged by malicious receiver J. The certificate holder H has no complete control over his signature and privacy of certificate holder is not achieved. It is clear that public key digital certificates cannot be used for authenticating certificate holder. This issue is addressed Generalized Digital Certificate (GDC) based scheme [2].
Generalized digital certificates are used to authenticate the certificate holder and establish a secret session key at each end of communication using any type of digitized general certificate like digital unique identity certificate, digital passport, digital school certificate, etc. A GDC consists of general and public information of the certificate holder and digital signature of this public information generated by certifying authority. GDC is never sent to the receiver and the signature of GDC will not be sent to the receiver in plain text. Rather GDC holder will have to respond to the challenge sent by the receiver.
In the GDC based scheme [2], only GDC holder is verified and a secret session key gets established upon successful authentication for subsequent communication. But there is no provision for sender to check the authenticity of the verifier. The proposed scheme described in this paper uses the concept of GDC and achieves mutual authentication along with session key establishment.
Digital Certificate application involves following three entities.
-
i. Certifying Authority (CA): is a third party which can be trusted by all others. CA can be an organization or a person who can create a digital signature using its private key PRCA . The X.509 public key digital certificate contains the public key of the certificate holder and digital signature of CA for this public key. The GDC consist of public information of certificate holder in the general form of certificate like digital unique identity certificate, digital passport, digital school certificate etc. and digital signature of CA for this public information. But there will be no public key present in GDC.
-
ii. GDC-Owner: is a person who receives the GDC for
his public information from a trusted CA through a secure communication. In order to get authenticated and establish a secret session key this GDC-Owner needs to present a valid response to the challenge generated by GDC-verifier.
-
iii. GDC-Verifier: is a person with whom GDC-Owner
wishes to establish a secure communication. GDC-Verifier sends a challenge to the GDC-Owner and verifies the response using received public information from GDC-Owner and public key of the CA.
The entire GDC is never sent to the GDC-Verifier instead the GDC-Owner will simply send the public information for which he or she obtained the digital signature from the CA. The digital signatures of GDC need not to be sent to the GDC-Verifier. The digital signature becomes a security factor on the basis of which user can be authenticated [2].
The rest of the paper is organized as follows. In section II an overview of the related work is given. Section III consists of proposed DL-based scheme and its security analysis. In Section IV the proposed IF-based protocol and its security analysis is discussed. Section V consists of the conclusion which is followed by references.
II. Related Work
Authentication is one of the most important services of security. Managing a key is also an important aspect of establishing a secure communication. A number of efforts have been taken to improve these services. Most of the techniques make use of public key digital certificates.
A receiver can validate the authenticity of a received message by validating the digital signature of the receiver. For this purpose Public key digital certificates are used. But this scheme may violate the privacy of a signer if receiver decides as explained previously.
Efforts have been taken for solving this issue with the introduction of signature scheme that will not depend on digital certificates for the verification of signatures [10], [11], [12], [13], [14]. In [15] concept of signatures that do not require certificates are proposed which uses benefits of ID based cryptography and it can be widely used in applications where there is less bandwidth like wireless applications [16]. This scheme has a drawback of the key escrow problem.
Another attempt was made to solve the issue of privacy violation in [8] with the help of Identity based cryptography in which identity of user like name or email address will be used as a public key. But it is limited to the situation in which user knows the identity of his communication partner.
Introduction of Generalized digital certificate [2] solves the problem of violation of user’s privacy. It is used to authenticate the certificate owner and establish a session key with communication partner. Generalized digital certificate consist of public information like digital birth certificate, school certificate, identity etc. of GDC-owner. The Generalized digital certificate is used to authenticate the GDC-owner by using challenge and response mechanism in which information of digital signature will be passed as a secret token. Generalized digital certificates provide only one way authentication. Both communication partners can’t be authenticated at once. If we authenticate a GDC-owner and after successful authentication if the same procedure is used by the user at the other end, then for his successful authentication it will take again four steps of the protocol described in [2]. For this step of the protocol in [2] will be doubled. At the end there will be two session keys.
Attempts have been taken in improving the Generalized Digital Certificate based communication [4
-
6] . In [4] there is improvement in strengthening session key created for each message being exchanged. It treats
the session key as a key1. Key1 will be used to send a message first time only. For the second time key2 will be obtained as
Key2= key1 XOR M1
Key3= key2 XOR M2
This will be continued until the session expires. But this scheme also works to achieve one way authentication.
In [5] data security is increased by use of AES. It is also based on one way authentication. Similar kind of work is found in [6] with an additional security feature but it is again based on one way authentication.
The proposed work consists modifications to Lein et al’s Discrete log based scheme (DL-based scheme) and Integer Factorization based scheme (IF-based scheme) in order to provide mutual authentication and subsequent session key establishment.
III. Dl-Based Scheme
In day to day life individuals are identified on the basis of ID-card issued by a trusted authority. The ID-card consists of name, date of birth, address etc. and photograph. The authority put a stamp and signature on photograph and ID-card. If a person produces an ID-card and matches with the photo on the card, then he or she is successfully identified. In this scheme, it is very difficult to forge signatures. So owning an ID-card (paper certificate) is the key factor in the process of identification.
The schemes described in this paper introduce a similar approach for identification of both individuals (one who is being verified and the other who is verifying). In the digital world, both individuals one who is being verified and other who is verifying present at far ends so authentication of both parties becomes important. In this new scheme, there is no need to transfer entire GDC to each other for authentication of each other rather a valid response to received challenge needs to be generated. Finally, on successful authentication of both individuals a secret session key is generated.
Like GDC the proposed protocol is based on the combination of traditional discrete log based ElGamal digital signature [3] and the famous Diffie-Hellman Assumption [9].
-
A. ElGamal Digital Signature
In the ElGamal scheme [3] a large prime number Q and its primitive root α is supposed to be shared by all the users [20]. The signer selects at random a private key X such that X е [1, Q - 2] and computes corresponding public key у = ах mod Q .
The signer then selects a random secrete k excluding 1 and Q-1 such that к Е Z у and computes R1 = a* mod Q [19] . Then S1 is solved by using the signer’s secrete X, and k, as
51 = JT^D - (RI * X))mod((? - 1) (1)
Where D represents the message digest of the message Msg . The digital signature of the message Msg is defined as a pair (R1, S1). The signature is verified by checking whether “(2)” holds true.
aD = y«L , filSlmod(2 (2)
The parameter R1 is computed offline which depends on random integer k. It is independent of the message Msg . So there will be no harm in making it public, but the parameter S1 depends on the user’s statement Msg. S o S1 should be kept secret. There are a number of variants of ElGamal Signature [17].
-
B. Diffie-Hellman Assumption
Assume U and V have their private keys X U and X V. Their corresponding public keys are Yu = aXumod Q and, Yv = a Xv mod Q respectively, where Q is a large prime number and α is its primitive root such that a e Z* of order Q. Only U and V can compute a shared secret key as DL-Based protocol for Authentication of the user and Establishment of Key
^U,V=yvxu madQ =УихУт<х1д =KVU (3)
Diffie-Hellman Assumption refers to the assumption that is computation of key KU, V from public key YU or YV, without knowledge of corresponding XU or XV is computationally infeasible. However, solving the private key X U or X V from the corresponding Y U or Y V is equivalent to solving the discrete logarithm problem.
-
C. Review of DL-based Authentication and Key Establishment
The scheme consists of two phases [2]:
-
i. Registration at Certificate Authority: Let O and V are the GDC-owner and GDC-Verifier. In order to get Authenticated O needs to be registered at Certifying Authority. O will send his public information M O like digital identity to the Certifying Authority and as a result O will receive a Generalized Digital Certificate having digital signature of Authority. Digital signature consists of a pair (R1 O , S1 O ) created by using ElGamal digital signature and private key of certificate Authority. As stated earlier R1 is made public, but S1 depends on public information MO. So it must be kept secret during and after the process of authentication. The protocol for authenticating and establishing a key is as described below.
-
ii. Authentication and Key Establishment Protocol: The protocol takes four steps to complete described as follows:
Step 1:
The user O needs to compute secrete token from digital signature of receiving Generalized Digital Certificate. It is calculated as below
$0 = 7?10sl° mod Q (4)
User O passes his public information MO and pair (R1O, $O) to the GDC-verifier V
Step 2:
After receiving these, verifier needs to verify whether the token received $ O is really generated from the digital signature of Generalized Digital Certificate of O. This can be done by checking whether the following “(5)” holds true.
aD„ . y«iD , $o mod q (5)
Where Y is the public key of the certificate authority. If inequality 5 doesn’t satisfy then authentication will fail and protocol stops otherwise V will select a random integer ZV such that Zv 6 [1 (? - 2] and computes a challenge CHV = Rl0Zv mod Q and sends CHV to the user O.
Step 3:
The user O uses secret S1 and computes Diffie-Hellman Key
Kov = CHy^mod Q
and obtains
K'0V=D
Step 4:
User V will receive CHc and ACK . User V uses his secrete Zv and computes Diffie-Hellman Key Kv 0 = $2vmod Q and obtains K'oy = D(K0,r) , and checks whether ACK = htj^CfivllCtfJ is true. If this satisfies then GDC-owner O is successfully authenticated by GDC-verifier V. Otherwise, authentication fails, and protocol stops. On successful authentication a session key is created.
SK = CHoZymodQ = CHvz°modQ (6)
-
D. Proposed Dl-Based Scehme
The proposed DL-based scheme provides mutual authentication on the basis of their public information like digital driving license, digital passport, or any digital identity. The proposed scheme consists of two phases:
-
• Registration at Certificate Authority
-
• Mutual Authentication and Key Establishment
This new scheme is based on discrete logarithm [7]. Solving the problem of discrete logarithm is computationally infeasible.
Select a large prime Q such that Q-1/2 is also a prime number [21]. Find its primitive root α. Prime number Q and α is supposed to be shared by all.
-
i. Registration At Certificate Authority
Initially, both users need to be registered at certificate authority. Certificate Authority will produce Generalized Digital Certificate for the received public information M O, and MV of user O and V respectively. O receives a signature pair (R1O, S1O) and V receives a signature pair (R1V, S1V) for their public information MO, and MV. The values S1O, S1V depends on public information so need to be kept secret.
-
ii. Mutual Authentication and Key Establishment phase
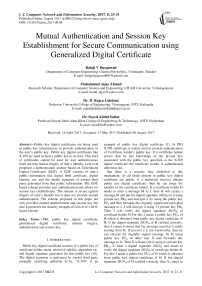
Authentication and key establishment protocol take five steps as shown below.
Step 1:
The user O needs to compute secrete token from digital signature of receiving Generalized Digital Certificate.
$0 = 7?1OS1° mod Q (7)
User O passes his public information Mq and pair (R1O, $ O ) to the GDC-verifier V.
The user V also computes his secret token from the information received during registration.
$p = (fll7)sl''?nod Q
Step 2:
The verifier needs to verify whether the token received $O is really generated from the digital signature of Generalized Digital Certificate of O. This can be done by checking whether “(8)” holds true.
aDo _ КЙ1О * $omod Q (8)
Where Y is the public key of the certificate authority. If inequality (8) doesn’t satisfy then authentication fails and protocol stops otherwise V selects a random integer ZV such that Zv E [L Q - 2] and computes a challenge
Cv = Rl0Zv mod Q . (9)
User V sends cV, M’ V , (r1V, $ V ) to o.
Step 3:
User O checks the validity of receiving credentials. This can be done through “(10)”.
qDv- =YR1v, $v,mod Q (10)
Where Y is the public key of the certificate authority. If inequality (11) doesn’t satisfy then authentication of V fails and protocol stops otherwise the user O randomly selects ZcE[Lt?-2]and computes
Со = (Rl0)z° mod Q (11)
CH0 = (flip) z°mod Q . (12)
User O uses secret S1 O and computes Symmetric key using DHA
K0-V = CHvSL°mod Q = flip ^SioSip mod Q (13)
User O obtains, K'ov = D(K0,v) where Л()М represents a key derivation procedure with ^D .V as an input. O computes acknowledgement using
ACK= h (K’ O, V , C V ||C O ). (14)
O sends an ACK, C O , and CH O to V
Step 4:
V computes symmetric key using DHA Kv0 = S0Zv mod Q and obtains K^ = ^fc), where D(^) represents a key derivation procedure. Owner O is authenticated if
ACK = h(K[,.o, Cp||C0) (15)
Otherwise, the authentication fails and protocol exits. V computes a key
Kv01 = CHoslv mod Q (16)
Obtain s ^v,oi — dQkV;OX) . Comput e a new ACK1, ACK1 =к(к^,ог. CHv||CH0||flK0) V sends ДСК1, CHV to O.
Step 5:
User O computes Kovi = $и mod Q and O derives another symmetric key ^o,vi — ^ Qkovx) which is used to compute AC KI which is used to authenticate V using “(17)”.
ACK1 =h(K'0VV Cp||C0||flaF) (17)
O creates a session key
SK = (Cr)ZDmod Q = (К10Уо2г mod Q (18)
Otherwise, the authentication fails and protocol exits. Meanwhile, user V creates session key
SK = (Co) Zymod Q = (fll0)z°Zr mod Q
Where ^R is a shared session key between O and V. In order to get authenticated successfully each user needs to compute the secret token and send public information along with a pair (R1X, $X) to each other. The validity of the digital signature will be checked with the help of “(2)”. In which RI51 is replaced by secrete token of another user. As every term in “(2)” is public, anyone can validate it, but for successful authentication of user received ACK and computed ACK must match each other and this is possible if and only if ACK is generated by genuine user who have authentic Generalized Digital Certificate because ACK is computed by using a key ^I'.D and A p p which requires secret Sip and secret Я p respectively. And only GDC-Holder can compute session key as security provided by Diffie-Hellman. In this way both parties can authenticate each other.
If a malicious user somehow manages to obtain the public information of V then there is no possibility of forgery attack on the identity of V because V sends challenge in step 2 which is obtained from the use of secret parameters of digital signature of the generalized digital certificate. And computation of secret S1 V from $ V is a discrete logarithmic problem which is infeasible. Also, the computation of session key requires the use of secret parameter S1 of public information MV and this is possible for only genuine user V who owned generalized digital certificate for his public information MV from certificate user.
-
E. Security Analysis Of Proposed Dl-Based Scehme
The security analysis of the newly introduced scheme is described in this section. The proposed scheme depends on Diffie-Hellman in combination with ElGamal digital signature. The security of his scheme depends on the security of Diffie-Hellman and security of ElGamal scheme. The proposed protocol satisfies the property of unforgeability, one-wayness, and non-transferability.
-
a) Unforgeability: User who knows the digital signature of Generalized Digital Certificate can generate a valid response only. In order to perform a forgery attack, an attacker needs to compute (R1 X , $ X ). If somehow attacker manages to get this pair and his digital signature gets validated by using “(8)” or “(10)”. This is possible because all values are public in these equations, attackers need to find out the secrete power S1 of from token $. This is infeasible because of the security provided by discrete
logarithm. Then in order to get successfully authenticated attacker needs to present a valid ACK which is infeasible. Only GDC-Holder can obtain the secret parameter S1 from certificate authority which is kept as a secret. Thus UNFORGEABILITY is achieved through the security of Diffie-Hellman in combination with ElGamal digital signature. In this way, the new proposed scheme is secure against Forgery attacks.
-
b) One-wayness: Based on the interactions nobody can derive the digital signature of the certificate. The digital signature of the generalized digital certificate consists of a pair (R1, S1). GDC-Holder is not
sending the generalized digital certificate to anybody, S1 will be secure. Instead of sending secret parameter token generated from secret parameter is passed. The computation of secret parameter S1 from $ is infeasible because this is equal to solve problem of discrete logarithm and which is infeasible. If attacker can’t obtain secret parameter S1 then he can’t respond with correct лек and protocol stops. In this way the proposed protocol satisfies the property of one-wayness.
-
c) Non-transferability: A response produced for one GDC-Verifier should not be transferred in response to the other GDC-Verifier. Because this will lead to the impersonation of a user. Because of Diffie-Hellman a valid response АСК is generated by GDC-Holder, who knows secrete parameter s1 or by a user who knows the random secret of random challenge. As the user selects a random challenge each time, the response validity is for only one session.
GDC-Holder is not sending the generalized digital certificate to anybody its digital signature will be safe and nobody can transfer complete generalized digital certificate to any other user. In this protocol, there is no problem of privacy intrusion. Therefore a valid response АСК cannot be passed into other GDC-Verifiers challenge.
KO,Vl = ^(^0,71)
IfACK1= h^K,vl, CyllCgll^J then V is Authenticated and
Creates a session key
Sx = (CF)z°moti Q
SK = (Rlo")ZoZvmodQ
SK = (Co) Zvmod Q = (Я1 o)ZoZy mod Q
Otherwise, the Authentication fails and protocol terminates
Fig.1. DL-based Mutual Authentication and Key Establishment Protocol
IV. If-Based Schme
This section describes a mutual authentication protocol which is based on the trapdoor hash based online- offline signature scheme and Diffie-Hellman assumption generalized modulo composite number (GDHA) [2], [2223]. The online-offline scheme makes use of the trapdoor hash function that satisfies the property of unforgeability, one-wayness and Non Transferability.
-
A. Review of IF-based User Authentication And Key Establishment
The protocol consists of two phases [2]:
-
i. Registration At Certificate Authority
-
ii. Authentication and Key Establishment
-
i. Registration at CA:
Certificate owner O sends his public information for registration to the certificate authority (CA). CA creates a GDC by putting his signature, which will be converted into the online-offline signature of the public information received. The CA sends GDC consisting of online-offline signature defined by
SifcM«, (ЬшН^ч^СМ’.Н’^.ЗЕС, hash^J^(.M,,R'')
The owner is required to keep the SEC secret from others. For verification owner sends a secret token computed from secret parameter SEC .
-
ii. Authentication and key establishment protocol
Step 1:
The user O needs to compute secrete token from digital signature of receiving Generalized Digital Certificate. It is calculated as $0 = g0SEC° mod n
User O passes his public information M O and Siflsignkey (^^^hasMtsyW '® )}-$0' hashhoj^jtey^M ,R ) to the GDC-verifier V
Step 2:
After receiving these, verifier needs to check the authenticity of the received token and information Initially, V checks the validity of the digital signature of
CA received by owner O. Verify
Si9sign_key (j^^haskjay^ >R )) using^^Sverifykey of CA, if it is verified then V check the hashhQ5kkey(M0,R0) = hash^^.CM'o.R^ (19)
If above inequality doesn’t satisfy then authentication fails and protocol stops otherwise V will select a random integer ZV such that Zve [1Л-1] and computes a challenge CHV = g0Zv mod N and sends CH¥ to O.
Step 3:
The user O uses secret SEC and computes Diffie-Hellman Key Kov = CHvSEC°mod N and obtains K'ov = D0w), where ^.f) represents a key derivation procedure with Ар у as an input. O selects a random integer ZO such that Zc e [1Л -1] and computes a challenge CH0 = goz° mod N and computes ACK = h(vKro,v-CHv\\CHo') , where h(K'0V.CHv\\CH0) represents a one way keyed hash function with Kg ,V as an input key. The user O then sends CH0 and ACK .
Step 4:
V will receive CHc and ACK . V uses his secret Zy and computes Diffie-Hellman Key KVj0 = ^mod N and obtains K'o.v = ^f) , and checks whether
ACK = /1(К^,СЯГ||СЯО) (20)
If this satisfies then GDC-owner O is successfully authenticated by GDC-verifier V. Otherwise, authentication fails, and protocol stops. On successful authentication a session key is created.
SK = CH02vmod N = CHVz° mod N (21)
-
B. Proposed IF-based Scheme
The new scheme consists of two phases:
-
i. Registration at CA:
Initially, both users need to be registered at certificate authority. CA will produce Generalized Digital Certificate for the received public information Afc , and AfF of user O and V respectively. O and V receive GDC having digital signature of the CA described as
Si9sign_key {^^^hushjcey^ -^ 5^iSECq, hosh^Qg^ ^^M ,R J and
respectively. The value , depends on public information so need to be kept secret.
-
ii. Mutual Authentication and key establishment protocol
Figure 2 shows the mutual authentication protocol for user authentication and key establishment.
Step 1:
The user O needs to compute secrete token from digital signature of receiving Generalized Digital Certificate. It is calculated as $o = 9oSEC° m°d n User O sends his public information MO and
Sigs^.k„ (hash^ ^(X.R'iyS-, hash^ ^M'.R”)
To the GDC-verifier V.
User V also uses his information received from the CA during the registration phase and computes his secret token $r. such that Sv = (доУ^’тпоД N
Step 2:
After receiving these, verifier needs to check the authenticity of the received token and information. Initially, V checks the validity of the digital signature of CA received by owner O. Verify
Si9sign_key {^^^hasb^key ^ >R )) using 5iSverify_key of CA, if it is verified then V check the ^0-5^кдзп_кеу^Мр1 Rq) hoshkttsk key ^^0*^0^
If above inequality doesn’t satisfy then authentication fails and protocol stops, otherwise V selects a random integer Z V such that ZVE [LJV-1] and computes CHv=9oZvmodN V sends to O challenge CHV and
Step 3:
The user O uses secret SEC and computes symmetric key using GDHA Kov = CHvSEC°mod N and obtains K'ov = °(^y), where ^(^.f) represents a key derivation procedure with Ар у as an input. O selects a random integer ZO such that Zc e [1Л -1] and computes a challenge CH0 = goz° mod N and computes ACK = Ь(Я^И,СЯГ||СЯО) , where ь(^г,СЯг||СЯ0) represents a one way keyed hash function with ^D .F as an input key. The user O then sends CH0 and ACK .
Step 4:
V will receive CHc and ACK . User V uses his secret Zy and computes symmetric Key Куд = $Zrmod N and obtains Ko,v = »(^f) , and checks
ACK = й(^0,СЯг||СЯ0)
Step
USER O
USER V
Creates a Secret Token
Se = (ggY^modN $r = (so)"CKmod N
Creates a
Secret Token
Si^^J^s^j^^
, MO
Verify signature SigIe,.k=, (hosh^^GV,»')} and hash^^LM-.R-) - Hash^^Mg.R'^
If authentication fails then the protocol terminates, otherwise Verifier randomly selects 2V | such that zv e [ln -1] and computes CHV = g^ modN
To check the authenticity of the received information the owner needs to derive a symmetric key which is obtained as ^OVl = $p2° mot^ N and obtains ^O,V1 = ^ (^o,ri) Create h (^o,vi • ^o.vi I l^o и) and compare it with ЛСК1 If it matches, and then V is authenticated and creates a session key
SK = (CHvYomod N = ^д0У°2у mod N (24)
Otherwise, the Authentication fails and the protocol terminates. Meanwhile V creates a session key
SK = CH о Zvmod N = CHV z°mod N
Я'}
Verify signature Sig,^^ [hash-.^.^(.M',R')) and hashtSMu_iec)XM5,R5') = hashL^u^^CA^.,^.)
If authentication fails then the protocol terminates, otherwise user O randomly selects Zo such that z„e LL-v-l] and computes
CH- = g-z" mod N and computesKoy = CHyK° modN and obtainsK*e,=DV^, computes ACK = h(^r,CHK| | CH^
C. Security Analysis of Proposed IF-Based Scheme
The IF-based protocol makes use of the GDHA, RSA signature, and online-offline signature based on the hash function. So the security of the scheme depends on the security of the GDHA, RSA signature and online-offline signature scheme. Similar to the security analysis given in section III E for the DL-based protocol, the IF-based scheme also satisfies the property of unforgeability, onewayness and non transferability.
CH- and ACK
computes KyA = $/v modN and obtains к;а = d IFACKl=h(<K^„,K,]V1\\K=]¥’) then V is Authenticated and Creates a session key S, = (,CHy)Z3modN =(.go)z°Zv modN S, = (СНоУ>т0а N- (So)rozv mod N Otherwise, the Authentication fails Fig.2. IF-based Mutual Authentication and Key Establishment Protocol If this satisfies then GDC-owner O is successfully authenticated by GDC-verifier V. Otherwise, authentication fails, and protocol stops. V again computes a new asymmetric key КИА1 = CH0SECv mod N and obtains Ky,01 — ^ (Лгди) Computes and sends ACK1 to O ЛС/fl =к(^1,^1||Крд) (23) Step 5: V. Conclusion Public key digital certificates are used for authenticity of public key of a user but it cannot be used for user authentication. Lein et al proposed generalized digital certificates based scheme which can be used to authenticate a user and establish session keys for secure communication. But it does not provide mutual authentication which is essential for many applications. The proposed work consists of modifications to DL-based and IF-based schemes. The proposed schemes not only achieve mutual authentication but also preserves the security strength of the original schemes.
Список литературы Mutual Authentication and Session Key Establishment for Secure Communication using Generalized Digital Certificate
- Network Working Group, "Internet X.509 public key infrastructure certificate and crl profile, RFC: 2459," Jan. 1999.
- LeinHarn and JianRen, "Generalized Digital Certificate For User Authentication And Key establishment for secure communication," IEEE Trans. on wireless communication,vol.,10,No.7,July2011.
- T. A. ElGamal, "A public-key cryptosystem and a signature scheme based on discrete logarithms," IEEE Trans. Inf. Theory, vol. 31, no. 4,pp. 469-472, 1985.
- Bismin.V.Sherif and Andrews Jose, "Secure Communication using generalized Digital Certificate", International Journal of Computer Applications Technology and Research, Volume 2-Issue 4,396- 399, 2013.
- M.V.Kishore, G.Pandit Samuel, N.AdityaSundar, M.Enayath Ali, Y.LalithaVarma "A Novel Methodology for Secure Communications and Prevention of Forgery Attacks," International Journal of Computer Applications (0975 – 8887) Volume 96– No.22, June 2014.
- SharinaToor, KesavaRaoSeerapu, Y.Rameshkumar, "A Novel Secured Data Communication and Prevention of Forgery Attacks Using Digital Certificates," international Journal of Computer Science and Information Technologies, Vol. 5 (5), 2014, 6410-6415.
- en.wikipedia.org/wiki/Discrete-logarithm
- A. Shamir, "Identity-based cryptosystems and signature schemes," in Advances in Cryptology: Proc. Crypto'84, Lecture Notes in Computer Science vol. 196, (Berlin), pp. 47-53, Springer-Verlag, 1985.
- W. Diffle and M. E. Hellman, "New directions in cryptography," IEEE Trans.Inf. Theory, vol. 22, pp. 644-654, 1976.
- W. Diffle and M. E. Hellman, "New directions in cryptography," IEEE Trans. Inf. Theory, vol. 22, pp. 644-654, 1976.
- M. Jakobsson, K. Sako, and R. Impagliazzo, "Designated verifier proofs and their applications," Advances in Cryptology - EUROCRYPT, pp. 143-154, 1996. LNCS Vol 1070.
- C. Schnorr, "Efficient signature generation by smart cards," J. Cryptology, vol. 4, no. 3, pp. 161-174, 1991.
- F. Laguillaumie and D. Vergnaud, "Designated verifier signatures: anonymity and efficient construction from any bilinear map." IACR eprint.
- R. Steinfeld, L. Bull, H. Wang, and J. Pieprzyk, "Universal designated verifier signatures," in Asiacrypt'03, vol. LNCS 2894, pp. 523-542, 2003.
- L. Harn, J. Ren, and C. Lin, "Design of DL-based certificateless digitalsignatures," J. Syst. Software, vol. 82, pp. 789-793, 2009.
- Al-Riyami, S., Paterson, K, "Certificateless public key cryptography,"Advancesin Cryptology – AsiaCrypt, LNCS, vol. 2894. Springer-Verlag, pp. 452–473, 2003.
- L. Harn and Y. Xu,"Design of Generalized ElGamal type digital Signature scheme based on discrete Logarithm," ELECTRONICS LETTERS, vol. 30 , no. 24, 1994,2025-2026.
- Rivest R. L.Shamir A. and Adelman L, "A Method for obtaining digital signatures and public key cryptosystems,"commun. SCM, 1978, 21, (2), pp.120-126.
- R. Lidl and H. Niederreiter, Finite Fields. Cambridge University Press, 2000.
- Rashmi singh, shiv kumar "Elgamal‟s Algorithm in Cryptography" International Journal of Scientific & Engineering Research Volume 3, Issue 12, December-2012.
- Pohlig, S. and M.E. Hellman, "An improved algorithm for computing logarithms over GF (p) and its cryptographic significance," IEEE Transactions on Information Theory, vol. IT-24, 1978, pp. 106-110.
- A. Shamir and Y. Tauman, "Improved online/offline signature schemes," in Proc. 21st Annual International Cryptology Conf. Advance Cryptology, p. 355-367, Springer-Verlag, 2001.
- H. Krawczyk and T. Rabin, "Chameleon signatures," in Proc. Symp. Netw. Distributed Syst. Security (NDSS00), (Internet Society), pp. 143-154, Feb.
- Dr. S. Santhosh Baboo,K. Gokulraj, "An Enhanced Dynamic Mutual Authentication Scheme for Smart Card Based Networks," I. J. Computer Network and Information Security, 2012, 4, 30-38.