Ключевые проблемы безопасности данных в мобильных приложениях
Автор: А. А. Грейс, Д. Р. Идрисова, Д. М. Скрябин
Журнал: Informatics. Economics. Management - Информатика. Экономика. Управление.
Рубрика: Информатика, вычислительная техника
Статья в выпуске: 4 (4), 2025 года.
Бесплатный доступ
В статье проведён комплексный анализ ключевых проблем обеспечения информационной безопасности мобильных приложений в условиях цифровой трансформации в контексте концепций Индустрии 4.0 /5.0. Рассмотрены основные угрозы, обусловленные уязвимостями программного кода, незащищёнными интерфейсами прикладного программирования, инъекциями вредоносного кода, атаками типа MitM, а также методами социальной инженерии и фишинговыми атаками. Рассмотрены сценарии эксплуатации уязвимостей – применения вредоносных библиотек, подмены сертификатов, использования небезопасных протоколов передачи данных (HTTP, FTP) и манипуляций с доверенной средой исполнения. Проанализированы ключевые аспекты защиты персональных данных и уязвимости облачных сервисов, связанные с ошибками конфигурации и проблемами механизмов разграничения доступа, в том числе в инфраструктурах AWS S3, Google Firebase и аналогичных платформах. Рассмотрены современные методы и технологии защиты, к которым относятся алгоритмы симметричного и асимметричного шифрования (AES-256, TLS 1.3, E2EE), применение сертификационного пиннинга, реализация многофакторной аутентификации (2FA, MFA), токенизация с использованием протокола OAuth 2.0, безопасные хранилища криптографических ключей (Android Keystore, iOS Secure Enclave). Отмечается важность использования архитектурной изоляции приложений и внедрения систем обнаружения вторжений и анализа поведения, основанных на машинном обучении. Особое внимание авторы уделяют переходу к концепции Zero Trust, предполагающей аутентификацию, минимизацию прав доступа и микросегментацию сетевых взаимодействий.
Мобильные приложенияинформационная безопасностьзащита данныхинъекцииMitMоблачные сервисымногофакторная аутентификациясимметричное и асимметричное шифрование, токенизация
Короткий адрес: https://sciup.org/14135083
IDR: 14135083 | DOI: 10.47813/2782-5280-2025-4-4-3022-3030
Текст статьи Ключевые проблемы безопасности данных в мобильных приложениях
DOI:
The current stage of societal development is characterized by a high degree of integration of information and communication technologies, as well as digital technologies, into key sectors of state infrastructure, leading to a significant transformation of management, production, and interaction processes. One of the most significant paradigms in the context of digital transformation is the Industry 4.0 concept – a trend toward automation and data exchange enabled by technologies such as cyberphysical systems, the Internet of Things, Big Data, machine learning and artificial intelligence algorithms, and distributed cloud computing. The goal of this paradigm is to build intelligent, adaptive, and self-regulating production and service systems that deliver high operational efficiency, predictive analytics, and autonomy. In this context, mobile devices become crucial elements of the digital ecosystem, serving as personal computing nodes, data gateways in the IoT environment, and universal human-machine interfaces for accessing distributed infrastructures, including industrial SCADA systems, cloud platforms, and secure corporate networks [1-2].
However, as digital infrastructure becomes more complex and dependence on algorithmically controlled processes grows, issues of resilience, ethics, and the human-centric nature of digital solutions are increasingly coming to the forefront. In this regard, the concept of Industry 5.0, which emphasizes the synergy between humans and machines, adaptability to external challenges, and the principles of sustainable development and digital humanism, is emerging as a response to the technocratically oriented Industry 4.0. Industry 5.0 focuses on creating more flexible, ethical, and inclusive technologies in which humans remain at the center of decision-making and interact with intelligent systems that support predictable and explainable outcomes. Approaches such as Explainable AI, cognitive computing, and humancentered interaction through Human-Computer Interfaces are actively used within this concept, where devices provide users not only with functionality but also with the ability to understand and control the actions of algorithms [3-5].
Mobile devices play a bridging role between the two paradigms, acting as universal interfaces for human interaction with the cyber-physical environment. Smartphones and mobile applications have evolved into personal computing centers integrated into complex digital ecosystems through IoT platforms and cloud computing. They perform critically important functions – ranging from smart home management via Zigbee and Bluetooth Low Energy technologies, providing access to medical data through Electronic Medical Record systems and health monitoring applications, to real-time interaction with industrial and financial systems through secure data exchange protocols such as MQTT and HTTPS. Mobile devices are integral components of both the Industry 4.0 architecture, supporting automation and real-time data collection, and the logic of Industry 5.0, where they serve as a link for integrating human-centric services with intelligent and autonomous systems.
Given the expanding range of mobile application functions and the volume of sensitive data they process, the importance of information security in the mobile environment increases significantly. Threats arising from software code vulnerabilities, improper API configurations, insecure data transmission, attacks on Trusted Execution Environments, and the use of third-party libraries can not only compromise the confidentiality and integrity of user information but also cause widespread disruptions in broader cyber-physical systems. Mobile applications have become the primary channel for users to interact with digital services, creating new challenges for ensuring data security. In the context of the ubiquitous use of smartphones and their integration into daily life, the security of information stored and processed on mobile devices has become a critical issue.
MATERIALS AND METHODS
The fundamental pillars of information security are confidentiality, integrity, and availability. Confidentiality ensures that sensitive data is protected from unauthorised access and remains private. Integrity involves maintaining the accuracy and consistency of information, preventing unauthorised alterations that could compromise its reliability. Availability guarantees that information and systems are accessible to authorised users whenever needed (Figure 1). These three elements collectively form the cornerstone of any information security strategy, and their protection is vital for both organizations and individuals alike [6-7].

Figure 1. Fundamental principles of information security.
Amid the rapid pace of digital transformation, cyber threats have become a significant concern for protecting key information security principles. Malicious software, cyberattacks, and unauthorized data access present serious dangers to the confidentiality, integrity, and availability of information systems. The evolution of information security has been shaped by numerous high-impact incidents, many of which have had far-reaching global effects, disrupting the operations of businesses, financial institutions, government bodies, and individual users. These cases underscore the growing complexity of cyber threats and the urgent need for comprehensive and adaptive security strategies.
Mobile applications, as a critical component of digital infrastructure, are increasingly targeted by cybercriminals due to the widespread adoption of smartphones and the vast amounts of personal and confidential data they handle. Key threats faced by mobile applications include software exploitation and malware injection, phishing and social engineering, data breaches caused by vulnerabilities in source code, and the use of unsecured communication channels vulnerable to interception (Figure 2) [8-9]. These risks underscore the need for robust security measures to safeguard both the applications themselves and the sensitive information they process.

Figure 2. Key threats.
RESULTS
Mobile application hacking
Mobile application hacking is a process aimed at compromising one of the three core aspects of information security: confidentiality, integrity, and availability of data. The goal of such hacking is to gain unauthorized access to application data, modify or destroy it, and disrupt the normal functioning of the system. Various techniques are employed during the hacking process, including reverse engineering, malware injection, exploitation of software and API vulnerabilities, as well as the use of fake certificates and Man-in-the-Middle attacks (figure 3) [10-11].

Figure 3. Key threats to mobile application hacking.
Reverse engineering is the analysis and decompilation of software to extract its source code or underlying algorithms (Figure 4). In the context of mobile applications, this process involves decompiling executable files of the operating system (e.g., APK for Android or IPA for iOS), analyzing resource and configuration files, and investigating cryptographic operations. Through reverse engineering, an attacker can discover security vulnerabilities in the application's implementation, as well as gain access to sensitive data such as session identifiers, credentials, encryption keys, user history, geolocation data, medical information, payment data, banking details, passwords and PIN codes, authentication and authorization tokens, device information, private messages and communications, as well as user settings.
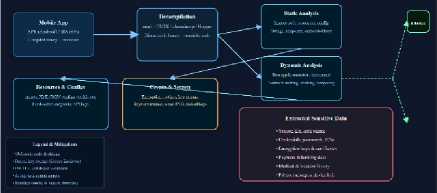
Figure 4. The process of reverse engineering a mobile application.
Various tools are used to perform reverse engineering, including JADX, APKTool, and Smali for Android applications, and Class-dump and Frida for iOS applications. These tools allow the examination of an app's structure, resources, and mechanisms for interacting with the operating system. During reverse engineering, vulnerabilities in the implementation of cryptographic algorithms may be discovered, enabling attackers to decrypt data if it is stored insecurely. Additionally, reverse engineering allows for the investigation of authentication, authorization, and data integrity verification mechanisms, identifying potential weaknesses that could be exploited to bypass protective mechanisms. For instance, discovering improper password storage or the use of weak hashing methods like MD5 or SHA1, which do not provide sufficient security levels, can significantly increase the risk of data compromise.
Malware injection is a technique used to insert unwanted instructions into an application with the aim of altering its normal behavior or executing malicious operations. Malicious code can be injected into an application through various methods, including exploits, API vulnerabilities, improperly configured input filters, library manipulation, interprocess communication attacks, vulnerabilities in third-party components and services, JavaScript injection in web applications, and attacks on plugin or extension systems. Exploits can take advantage of vulnerabilities such as buffer overflows, unsafe input/output functions, data handling errors, or improper authentication mechanisms. For example, a buffer overflow can lead to arbitrary code execution, giving the attacker remote access to the device. API vulnerabilities can be exploited to inject malicious code into unprotected client-server communication channels. An example is the lack of proper validation of input request parameters, which can lead to SQL injection or shell command injection attacks. Improperly configured input filters such as insufficient validation or sanitization of input data enable attackers to insert malicious data, such as SQL queries or server commands, potentially compromising data. Manipulating the libraries used by the application allows attackers to replace or modify third-party libraries, substituting them with compromised versions that contain embedded malicious code. This can disrupt application functionality or lead to data leakage. Inter-process communication attacks can inject malicious data via insecure channels between processes. JavaScript injection in web applications can lead to Cross-Site Scripting (XSS) attacks, in which attackers inject malicious scripts into webpages. When executed in the victim's browser, the script can steal session data or personal information. Plugins and extensions, especially if not thoroughly vetted for security, can be modified to carry out malicious actions, such as stealing confidential data or enabling remote access to the system.
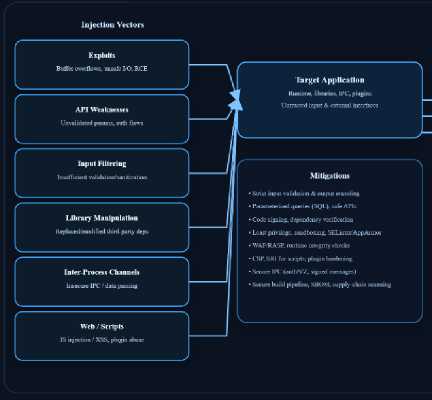
Figure 5. Malware injection.
Exploitation of vulnerabilities in software and APIs involves taking advantage of weaknesses in a system to gain unauthorized access, control, or manipulation of data and resources. In mobile applications, exploitation of vulnerabilities can manifest as buffer overflows (allowing attackers to insert arbitrary code into the application's memory) or insecure data storage, enabling access to sensitive information. Other common attack vectors include lack of input validation, which allows attackers to input data that can be used to manipulate the application's behavior, or errors in the implementation of authentication and authorization mechanisms that fail to properly verify user permissions. In the context of APIs, exploitation often focuses on SQL injection, where malicious code is inserted into database queries, as well as the absence of or weak protection against unauthorized requests. This allows attackers to perform actions on behalf of another user. Another significant risk is the use of unsecured data exchange protocols (such as HTTP instead of HTTPS), which allows attackers to intercept sensitive data in transit .
Man-in-the-Middle (MitM) is a method of intercepting, modifying, or replacing data transmitted between two parties . In the context of mobile applications, an attacker can position themselves between the mobile device and the server, controlling or altering the traffic that is typically sent over secure communication channels.
Malware
Malware is software designed to perform harmful actions on a user's device. The main types of malware include viruses, worms, trojan, spyware, adware and rootkits (figure 6) [12-13].
Figure 6. The main types of malware.
Viruses are a type of malicious software that inject themselves into other executable files or applications with the intent to propagate and perform harmful actions. Mobile viruses are typically spread via third-party applications installed from untrusted sources or through vulnerabilities in the operating system. They can corrupt files, disrupt device functionality, and steal sensitive data, potentially leading to data breaches or malfunctions in mobile applications.
Worms are standalone malicious programs capable of self-replication and spreading across networks without user interaction. They exploit vulnerabilities in operating systems or applications to propagate, often via the internet, infecting other devices and services, and may also be used to launch attacks on server infrastructures.
Trojan horses are malicious programs disguised as legitimate applications to deceive users into installing them. Once successfully deployed, trojans can exfiltrate personal data, transmit sensitive information to threat actors, or provide remote access to the infected device, enabling further attacks or data theft.
Spyware is designed for covert surveillance, monitoring the user's activity without their knowledge or consent. It can capture keystrokes, track browsing habits, and gather other personal information.
Adware delivers unsolicited advertisements to users, often without their explicit permission. In some cases, adware may be leveraged to covertly harvest data or redirect users to fraudulent websites, increasing the risk of phishing attacks. Moreover, excessive advertising can degrade device performance and hinder the operation of legitimate applications.
Screen lockers are a type of ransomware that restricts user access to a device or its data and demands payment to restore access. These threats can render a device unusable until the ransom is paid, often accompanied by intimidation tactics.
Rootkits are stealthy malicious tools that integrate deeply into the operating system to conceal the presence and activity of other malware. They provide persistent, unauthorized access and are notoriously difficult to detect and remove due to their low-level system integration.
Phishing Attacks and Social Engineering
Phishing is one of the most prevalent forms of social engineering, in which cybercriminals attempt to obtain access to users' confidential information fraudulently. This technique typically involves the creation of spoofed login pages, applications, or messages that closely mimic legitimate services. The primary objective of such attacks is to deceive the user into disclosing sensitive data. One of the most commonly used phishing techniques is SMS phishing, or smishing, in which attackers distribute deceptive messages that contain false alerts. These messages often include links to counterfeit websites designed to resemble official platforms visually, but which are in fact fraudulent. Users who fail to verify the authenticity of these links may unwittingly enter their credentials or personal information, thereby compromising their security. Another method is voice phishing, or vishing, in which attackers impersonate customer support representatives and attempt to trick victims into revealing verification codes sent via SMS or other sensitive personal data.
Data Leaks Due to Code Vulnerabilities
Data leaks stemming from source-code vulnerabilities represent one of the most critical security threats to mobile applications. Such vulnerabilities typically arise from flaws introduced during the software development lifecycle, where inadequate data protection or improper handling of sensitive information leave the system vulnerable to attacks.
One of the most common causes of data leaks is insufficient validation of user input. Flaws in input validation can be exploited by attackers to inject specially crafted data, leading to unintended behavior of the application. For example, the absence of proper input sanitization can lead to SQL injection vulnerabilities, enabling unauthorized access to the application's database.
Another frequent cause of data exposure is insecure data storage. Storing sensitive information such as passwords or API keys in plaintext – whether in a database or in local files – without applying cryptographic protection significantly increases the risk of data compromise. When a mobile application fails to implement robust encryption mechanisms to protect confidential data, that information can be easily intercepted or extracted by malicious actors.
Weak authentication and authorization mechanisms also pose a significant threat. Misconfigured access controls or the use of weak passwords may allow attackers to gain unauthorized access to protected resources. For instance, failure to enforce proper rolebased access control or multi-factor authentication can result in unauthorized logins and data breaches.
Session management flaws represent another major risk. Poorly implemented session handling mechanisms can lead to session hijacking, granting attackers unauthorized access to user-specific data and functionalities.
Additionally, the use of outdated or vulnerable third-party libraries further increases the attack surface. These dependencies may contain well-known security flaws, which, if unpatched, can be exploited to compromise the entire application.
Problems of Storing and Processing Personal Information
Modern mobile applications actively process and store users' personal data, which, in the context of growing cyber threats, requires special attention to information security. Flaws in data storage architecture, vulnerabilities in cloud services, as well as misuse of access to confidential information by third-party applications pose significant risks that can lead to data breaches.
One of the most common vulnerabilities in mobile applications is the insecure storage of sensitive information directly on the client device. In the absence of proper protection mechanisms, such data becomes vulnerable to compromise when there is physical or software access to the device's file system.
The most frequent violations include the storage of passwords, access tokens (e.g., JWT, OAuth tokens), personal identifiers, and session keys in an unencrypted form in default storage systems such as SharedPreferences (Android) and UserDefaults (iOS). These mechanisms are serialized XML/Plist files, which can be easily read when root or jailbreak access is available. Furthermore, even without direct access to the file system, these data can be extracted through debugging interfaces (e.g., ADB, Xcode Debugger) or dynamic analysis tools (e.g., Frida, MobSF).
An additional source of leaks can be logging sensitive information to system logs (e.g., Logcat,
NSLog) as well as the use of insecure temporary storage (e.g., temporary files in /cache, /tmp, getCacheDir(), NSTemporaryDirectory()). Such data can be intercepted not only in the case of physical access but also when malicious software is installed that exploits vulnerabilities to bypass the app sandboxing system.
As an example, we can refer to the incident with UC Browser, where authentication data was stored in clear text in local XML files, as well as the case with Clubhouse, where audio data was transmitted and stored without proper encryption, potentially allowing third parties to gain access to it.
To prevent such threats, it is recommended to use secure storage mechanisms such as Android Keystore and iOS Keychain, which provide hardware-based encryption of keys tied to a specific device and/or biometric authentication. Additionally, logging sensitive data should be avoided, secure coding practices (e.g., obfuscation, file system access control) should be used, and a data deletion policy should be implemented when the app is closed or the user logs out.
Threats related to cloud services and APIs pose significant risks to the security of mobile applications, as many rely on cloud platforms such as Amazon Web Services (AWS S3), Google Firebase, and others for data storage and processing. Inadequate protection of these components can result in large-scale data breaches, often due to misconfigurations in access control settings. One of the most common causes of incidents is improper access control configuration, which makes data accessible to unauthorized users. Specifically, open databases, lack of proper authentication, and exposed API keys become entry points for attackers, significantly increasing the risk of data leaks. An example of such an incident occurred in 2020 with Firebase, where configuration errors led to the exposure of over 100 million user records. In this case, improperly configured access rules allowed unauthorized users to access sensitive data, highlighting vulnerabilities in access management processes on cloud platforms.Similar incidents could also be caused by open access to data storage in AWS S3 or the accidental posting of API keys in public repositories, such as GitHub, which enables attackers to use these keys for unauthorized access to cloud service resources.
An additional risk vector is the excessive request for permissions by third-party applications. Often, applications request access to contacts, geolocation, or the camera without a legitimate need, enabling them to collect sensitive information. This is particularly common in apps that incorporate advertising SDKs, which can extract metadata, browsing history, and personal user data. Such practices violate the principle of data minimization, which emphasizes collecting only the data necessary for the functionality of the application.
DISCUSSION
In response to the identified threats, various technical and organizational measures are being developed and implemented to enhance the security of user data. One of the key mechanisms for protecting personal data is encryption, which is applied both during data storage and transmission. To protect locally stored information, symmetric encryption using the AES-256 algorithm is preferred, as it provides a high level of security for data stored on the device. To ensure security during data transmission, End-to-End Encryption (E2EE) is recommended, where data is encrypted on the sender's device and decrypted only on the recipient's device, preventing anyone, including the network operator, from accessing it. Examples of E2EE usage include messaging apps such as Signal and WhatsApp. To protect data transmission between the client and the server, TLS 1.3 protocol should be used, which secures traffic against "man-in-the-middle" (MITM) attacks. Additionally, certificate pinning allows the client to verify the authenticity of the server's certificate and prevents the use of fraudulent certificates.
To enhance security and protect against unauthorized data access, mobile applications should implement multi-factor authentication (2FA). Under this mechanism, in addition to the password, the user must verify their identity using an additional factor, such as a one-time temporary code (TOTP), push notifications, or biometric data (e.g., fingerprints or Face ID). Biometric authentication provides a high level of protection because each user's biometric characteristics are unique. For additional protection, tokenization is used, where sensitive data is replaced with unique identifiers that have no value outside of the system. The OAuth 2.0 protocol allows access to services through temporary tokens, minimizing the risk of leaking login and password credentials and limiting access based on time and privileges. In systems like Apple Pay, dynamic CVC codes are generated for each transaction, which enhances security.
One important aspect of data protection is the use of specialized secure storage for cryptographic keys and other critical information. For example, the Secure Enclave on iOS devices and the Android Keystore on Android devices provide secure key storage in an environment isolated from the main operating system, making them inaccessible to attackers, even if the device is compromised. Additionally, mobile applications should use architectural isolation at the operating system level, known as sandboxing. This approach isolates apps from one another, preventing one app from accessing data owned by another, and reduces the risk of malware spreading. An effective complement to this is the implementation of continuous monitoring of app activity, which can detect anomalies, such as suspicious API requests or attempts at unauthorized access to confidential information, enabling a swift response to security threats.
Additionally, several other methods enhance personal data security. For example, using secure storage for sensitive information such as passwords and cryptographic keys, such as Secure Enclave and Android Keystore, helps isolate data from the main operating system. Data masking, in which sensitive information is replaced with partially encrypted or anonymized values, also helps minimize the risk of data leaks. The implementation of security monitoring systems and anomaly detection enables timely identification and blocking of suspicious activities, such as unusual API requests or unauthorized access attempts.
Regular updates of mobile applications and operating systems to fix known vulnerabilities are also an important step in ensuring security. Using vulnerability management platforms enables risk analysis and vulnerability elimination, helping prevent potential attacks. The implementation of session management mechanisms, such as automatic logouts after a certain period of inactivity or limiting session duration, reduces the risk of unauthorized access. Additional measures, such as checking user activity, using CAPTCHA, or confirming actions during suspicious access attempts, can enhance session security.
Furthermore, an important data protection principle is the principle of least privilege, which requires that users and applications be granted access only to the data necessary for their functions. Restricting access rights based on the principle of least privilege helps reduce the risks of data leaks and unauthorized use. Code obfuscation, which hides an application's internal logic, is also an important step in protecting against reverse engineering and the exploitation of vulnerabilities.
The application of these protection methods helps minimize the risks associated with security threats in mobile applications and ensures reliable protection of users' personal data, in compliance with modern privacy and security standards.
CONCLUSION
Given the constantly evolving threats and the increasing volume of data being processed, the challenges of protecting mobile applications are becoming increasingly complex. In the coming years, key directions will include the use of artificial intelligence, the development of new cryptographic standards and security architectures, and the evolution of authentication methods. AI and machine learning are already being used to analyze the behavior of mobile applications and users to detect anomalies. Modern security systems can learn from millions of interaction scenarios, identifying even non-standard patterns typical of malicious activity. For example, AI can automatically detect when an app suddenly starts sending data to an unknown server or requests atypical permissions. This allows threats that have not yet been classified by traditional antivirus databases to be blocked in real-time. Personalized AI models are especially effective in corporate environments, where user behavior follows stable patterns. Moreover, using AI to analyze user activity helps identify not only known threats but also new forms of attacks, making the security system more dynamic and adaptive.
Although quantum technologies are still in the early stages of development, their application to mobile security holds significant promise. Quantum encryption, based on the principles of quantum superposition and entanglement, provides theoretically absolute protection for transmitted data. The development of compact quantum keys and the integration of quantum random number generation (QRNG) into mobile chips could significantly enhance the cryptographic resilience of devices. Companies and research centers are already working on adapting quantum protocols such as BB84 for mobile platforms. These protocols ensure information transfer using quantum states, making interception or hacking impossible because any attempt to measure the data alters the transmitted information. In the future, this could become a critically important element of protection in the era of quantum computers capable of breaking classical cryptography.
The Zero Trust approach, which is based on constant authentication checks and minimizing access rights, is increasingly being implemented in mobile architecture. It operates on the principle of "trust no one by default" - every access request is verified independently, even if the device is already authorized. This reduces the risk of internal attacks and increases resilience to session hijacking, as each request to the system requires authentication confirmation. Meanwhile, Confidential Computing technologies provide data protection during processing - so even the operating system has no access to the encrypted data, which is processed in isolated environments. These technologies use protected computing environments (e.g., protected memory areas such as trusted execution environments), preventing access even by those with system privileges. These technologies are particularly important in mobile banking and healthcare applications, where data confidentiality is critical.
Modern authentication methods are moving away from passwords towards more reliable and convenient mechanisms. Contactless technologies such as facial recognition, iris scanning, or fingerprint identification are being actively integrated into mobile devices. These methods rely on biometric characteristics, which are unique to each user and difficult to forge. Alongside these, behavioral strategies are emerging, which analyze characteristic user behavior: typing speed, device tilt angle, screen scrolling patterns. These methods are hard to spoof, especially when combined with multi-factor authentication that uses multiple independent factors (e.g., biometric data and PIN code). In the future, such authentication methods may become the primary means of identification, enhancing security without compromising usability. Combined with AI and machine learning, these systems can adapt to changing user behavior patterns, making them even more resistant to attacks.


